Obtaining certifications can be challenging, but with the correct approach and the right resources, you can pass them successfully. These certifications are well-respected and serve as proof of a candidate’s abilities. One example of such a certification is the Certified Cloud Security Professional (CCSP) credential, a collaboration between (ISC)² and the Cloud Security Alliance (CSA). It is designed to verify that cloud security professionals possess the necessary knowledge, skills, and capabilities in areas like cloud security design, implementation, architecture, operations, controls, and compliance with regulatory standards.
The Certified Cloud Security Professional (CCSP) Exam is known for being tough because it covers a lot of cloud security ideas, rules, and top methods. This test needs you to really get cloud security and show that you can use what you know in real-life situations.
To prepare for the CCSP Exam, candidates should have a strong understanding of the domains mentioned above, along with practical experience in cloud security. Candidates can use study materials, including official study guides, practice exams, and online training courses to prepare for the exam. Hands-on experience with cloud security projects can also be valuable in preparing for the exam. Let us dig deeper into the exam details and then begin with the preparation resources.

About Certified Cloud Security Professional (CCSP) Exam
(ISC)² and the Cloud Security Alliance (CSA) created the Certified Cloud Security Professional (CCSP) certification to make sure that cloud security experts have the right knowledge, skills, and capabilities in areas like cloud security design, setup, structure, operations, controls, and following regulatory rules.
A CCSP demonstrates proficiency in cloud security architecture, design, operations, and service orchestration while applying information security skills to a cloud computing context. This professional competence is evaluated in comparison to a body of knowledge that is widely acknowledged. The CCSP is a stand-alone certification that supports and expands upon already available credentials and training courses, such as the CSA’s Certificate of Cloud Security Knowledge and the Certified Information Systems Security Professional (CISSP) from (ISC)2 (CCSK).
So, now that we have understood what is the certification about, lets move to our next step of gathering the basic details related to the exam.
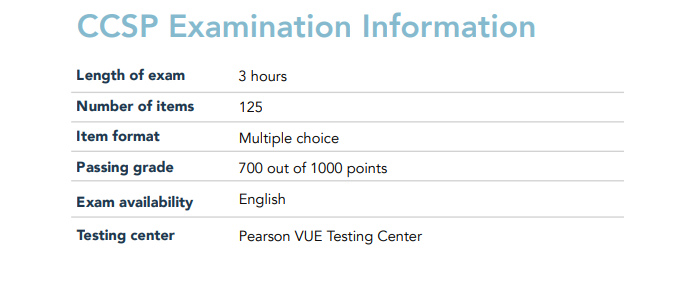
CCSP Exam Format
Details matter while considering taking the test. It is usually a good idea to be aware of the exam’s specifics in advance because the CCSP Test Difficulty is especially high. It might take you three hours to finish the exam. Also, there are 125 multiple-choice questions in the exam. Moreover, the CCSP Test Questions are only available in English. Above all, to obtain the CCSP Test Passing Score, you must accumulate a minimum of 700 points out of a possible 1000.
Prerequisites for the Exam
Obtaining CCSP certification is not an easy feat. To begin your voyage in CCSP certification course, you must have:
- First, you should have a minimum of five years of IT work experience, including three years in information security and at least one year in cloud security.
- Second, if you don’t have enough experience to become a CCSP, you can still become an Associate of (ISC)² by passing the CCSP exam. After that, you’ll have six years to gain the required five years of experience.
After this, there comes an important step of knowing the detailed course outline for the exam. Let us jump-start with the guidelines provided to choose your learning path.
CCSP Exam Outline
The CCSP exam course provides descriptive details about the topics covered in the exam. Also, it helps you familiarise with the CCSP Exam Pattern. The exam topics are:
Domain 1: Cloud Concepts, Architecture and Design 17%
Understand Cloud Computing Concepts
- Cloud computing definitions
- Cloud computing roles and responsibilities (e.g., cloud service customer, cloud service provider, cloud service partner, cloud service broker, regulator)
- Key cloud computing characteristics (e.g., on-demand self-service, broad network access, multi-tenancy, rapid elasticity and scalability, resource pooling, measured service)
- Building block technologies (e.g., virtualization, storage, networking, databases, orchestration)
Describe Cloud Reference Architecture
- Cloud Computing Activities
- Cloud Service Capabilities (e.g., application capability types, platform capability types, infrastructure capability types)
- Then, Cloud Service Categories, Infrastructure as a Service (IaaS), Platform as a Service (PaaS))
- Cloud deployment models (e.g., public, private, hybrid, community, multi-cloud)
- Cloud shared considerations (e.g., interoperability, portability, reversibility, availability, security, privacy, resiliency, performance, governance, maintenance and versioning, service levels and service-level agreements (SLA), auditability, regulatory, outsourcing)
- Impact of related technologies (e.g., data science, machine learning, artificial intelligence (AI), blockchain, Internet of Things (IoT), containers, quantum computing, edge computing, confidential computing, DevSecOps)
Understand Security Concepts Relevant to Cloud Computing
- Cryptography and key management
- Identity and access control (e.g., user access, privilege access, service access)
- Data and media sanitization (e.g., overwriting, cryptographic erase)
- Network security (e.g., network security groups, traffic inspection, geofencing, zero trust network)
- Virtualization security (e.g., hypervisor security, container security, ephemeral computing, serverless technology)
- Common threats
- Security hygiene (e.g., patching, baselining)
Understand the Design Principles of Secure Cloud Computing
- Cloud secure data lifecycle
- Cloud-based business continuity (BC) and disaster recovery (DR) plan
- Business impact analysis (BIA) (e.g., cost-benefit analysis, return on investment (ROI))
- Functional security requirements (e.g., portability, interoperability, vendor lock-in)
- Security considerations and responsibilities for different cloud categories (e.g., Software as a Service (SaaS), Infrastructure as a Service (IaaS), Platform as a Service (PaaS))
- Cloud design patterns (e.g., SANS security principles, Well-Architected Framework, Cloud Security Alliance (CSA) Enterprise Architecture)
- DevOps security
Evaluate Cloud Service Providers
- Verification against criteria (e.g., International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 27017, Payment Card Industry Data Security Standard (PCI DSS))
- System/subsystem product certifications (e.g., Common Criteria (CC), Federal Information Processing Standard (FIPS) 140-2)
Domain 2: Cloud Data Security 20%
Describe Cloud Data Concepts
- Cloud Data Life Cycle Phases
- Data Dispersion
- Data flows
Design and Implement Cloud Data Storage Architectures
- Storage types (e.g., long-term, ephemeral, raw storage)
- Threats to storage types
Design and Apply Data Security Technologies and Strategies
- Encryption and key management
- Hashing
- Data obfuscation (e.g., masking, anonymization)
- Tokenization
- Data loss prevention (DLP)
- Keys, secrets and certificates management
Implement Data Discovery
- Structured data
- Unstructured data
- Semi-structured data
- Data location
Implement Data Classification
- Data classification policies
- Data mapping
- Data labeling
Design and Implement Information Rights Management (IRM)
- Objectives (e.g., data rights, provisioning, access models)
- Appropriate Tools (e.g., issuing and revocation of certificates)
Plan and Implement Data Retention, Deletion and Archiving Policies
- Data Retention Policies
- Then, Data Deletion Procedures and Mechanisms
- Data Archiving Procedures and Mechanisms
- Legal Hold
Design and Implement Auditability, Traceability and Accountability of Data Events
- Definition of Event Sources and Requirement of Identity Attribution
- Logging, Storage and Analysis of Data Events
- Chain of Custody and Non-repudiation
Domain 3: Cloud Platform & Infrastructure Security 17%
Comprehend Cloud Infrastructure Components
- Physical Environment
- Network and Communications
- Compute
- Virtualization
- Storage
- Management Plane
Design a Secure Data Center
- Logical Design (e.g., tenant partitioning, access control)
- Physical Design (e.g. location, buy or build)
- Environmental design (e.g., Heating, Ventilation, and Air Conditioning (HVAC), multi-vendor pathway connectivity)
- Design resilient
Analyze Risks Associated with Cloud Infrastructure
- Risk Assessment and Analysis
- Cloud Vulnerabilities, Threats and Attacks
- Risk mitigation strategies
Design and Plan Security Controls
- Physical and environmental protection (e.g., on-premises)
- System, storage and communication protection
- Identification, authentication and authorization in cloud environments
- Audit mechanisms (e.g., log collection, correlation, packet capture)
Plan Disaster Recovery (DR) and Business Continuity (BC)
- Business continuity (BC) / disaster recovery (DR) strategy
- Business requirements (e.g., Recovery Time Objective (RTO), Recovery Point Objective (RPO), recovery service level)
- Creation, implementation and testing of plan
Domain 4: Cloud Application Security 17%
Advocate Training and Awareness for Application Security
- Cloud Development Basics
- Common Pitfalls
- Common Cloud vulnerabilities (e.g., Open Web Application Security Project (OWASP) Top-10, SANS Top-25)
Describe the Secure Software Development Life Cycle (SDLC) Process
- Business Requirements
- Phases and methodologies (e.g., design, code, test, maintain, waterfall vs. agile)

Apply the Secure Software Development Life Cycle (SDLC)
- Cloud-specific risks
- Threat modeling (e.g., Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege (STRIDE), Damage, Reproducibility, Exploitability, Affected Users, and Discoverability (DREAD), Architecture, Threats, Attack Surfaces, and Mitigations (ATASM), Process for Attack Simulation and Threat Analysis (PASTA))
- Avoid common vulnerabilities during development
- Secure coding (e.g., Open Web Application Security Project (OWASP) Application Security
- Verification Standard (ASVS), Software Assurance Forum for Excellence in Code (SAFECode))
- Software configuration management and versioning
Apply Cloud Software Assurance and Validation
- Functional and non-functional testing
- Security testing methodologies (e.g., blackbox, whitebox, static, dynamic, Software Composition Analysis (SCA), interactive application security testing (IAST))
- Quality assurance (QA)
- Abuse case testing
Use Verified Secure Software
- Securing application programming interfaces (API)
- Supply-chain management (e.g., vendor assessment)
- Third-party software management (e.g., licensing)
- Validated open-source software
Comprehend the Specifics of Cloud Application Architecture
- Supplemental security components (e.g., web application firewall (WAF), Database Activity Monitoring (DAM), Extensible Markup Language (XML) firewalls, application programming interface (API) gateway)
- Cryptography
- Sandboxing
- Application virtualization and orchestration (e.g., microservices, containers)
Design Appropriate Identity and Access Management (IAM) Solutions
- Federated identity
- Identity providers (IdP)
- Single sign-on (SSO)
- Multi-factor authentication (MFA)
- Cloud access security broker (CASB)
- Secrets management
Domain 5: Cloud Security Operations 16%
Implement and Build Physical and Logical Infrastructure for Cloud Environment »
- Hardware specific security configuration requirements (e.g., hardware security module (HSM) and Trusted Platform Module (TPM))
- Installation and configuration of management tools
- Virtual hardware specific security configuration requirements (e.g., network, storage, memory, central processing unit (CPU), Hypervisor type 1 and 2)
- Installation of guest operating system (OS) virtualization toolsets
Operate Physical and Logical Infrastructure for Cloud Environment
- Access controls for local and remote access (e.g., Remote Desktop Protocol (RDP), secure terminal access, Secure Shell (SSH), console-based access mechanisms, jumpboxes, virtual client)
- Secure network configuration (e.g., virtual local area networks (VLAN), Transport Layer Security (TLS), Dynamic Host Configuration Protocol (DHCP), Domain Name System Security Extensions (DNSSEC), virtual private network (VPN))
- Network security controls (e.g., firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), honeypots, vulnerability assessments, network security groups, bastion host)
- Operating system (OS) hardening through the application of baselines, monitoring and remediation (e.g., Windows, Linux, VMware)
- Patch management
- Infrastructure as Code (IaC) strategy
- Availability of clustered hosts (e.g., distributed resource scheduling, dynamic optimization, storage clusters, maintenance mode, high availability (HA))
- Availability of guest operating system (OS)
- Performance and capacity monitoring (e.g., network, compute, storage, response time)
- Hardware monitoring (e.g., disk, central processing unit (CPU), fan speed, temperature)
- Configuration of host and guest operating system (OS) backup and restore functions
- Management plane (e.g., scheduling, orchestration, maintenance)
Implement operational controls and standards (e.g., Information Technology Infrastructure Library (ITIL), International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 20000-1)
- Incident management
- Problem management
- Release management
- Deployment management
- Configuration management
- Service level management
- Availability management
- Capacity management
Support Digital Forensics
- Forensic Data Collection Methodologies
- Evidence Management
- Collect, Acquire and Preserve Digital Evidence
Manage Communication with Relevant Parties
- Vendors
- Customers
- Partners
- Regulators
- Other Stakeholders
Manage Security Operations
- Forensic data collection methodologies
- Evidence management
- Collect, acquire, and preserve digital evidence
- Security operations center (SOC)
- Intelligent monitoring of security controls (e.g., firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), honeypots, network security groups, artificial intelligence (AI))
- Log capture and analysis (e.g., security information and event management (SIEM), log management)
- Incident management
- Vulnerability assessments
Domain 6: Legal, Risk and Compliance 13%
Articulate Legal Requirements and Unique Risks within the Cloud Environment
- Conflicting international legislation
- Evaluation of legal risks specific to cloud computing
- Legal framework and guidelines
- eDiscovery (e.g., International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 27050, Cloud Security Alliance (CSA) Guidance)
- Forensics requirements

Understand Privacy Issues
- Difference between contractual and regulated private data (e.g., protected health information (PHI), personally identifiable information (PII))
- Country-specific legislation related to private data (e.g., protected health information (PHI), personally identifiable information (PII))
- Jurisdictional differences in data privacy
- Standard privacy requirements (e.g., International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 27018, Generally Accepted Privacy Principles (GAPP), General Data Protection Regulation (GDPR))
- Privacy Impact Assessments (PIA)
Understand Audit Process, Methodologies, and Required Adaptations for a Cloud Environment
- Internal and external audit controls
- Impact of audit requirements
- Identify assurance challenges of virtualization and cloud
- Types of audit reports (e.g., Statement on Standards for Attestation Engagements (SSAE), Service Organization Control (SOC), International Standard on Assurance Engagements (ISAE))
- Restrictions of audit scope statements (e.g., Statement on Standards for Attestation Engagements (SSAE), International Standard on Assurance Engagements (ISAE))
- Gap analysis (e.g., control analysis, baselines)
- Audit planning
- Internal information security management system
- Internal information security controls system
- Policies (e.g., organizational, functional, cloud computing)
- Identification and involvement of relevant stakeholders
- Specialized compliance requirements for highly-regulated industries (e.g., North American Electric Reliability Corporation / Critical Infrastructure Protection (NERC / CIP), Health Insurance Portability and Accountability Act (HIPAA), Health Information Technology for Economic and Clinical Health (HITECH) Act, Payment Card Industry (PCI))
- Impact of distributed information technology (IT) model (e.g., diverse geographical locations and crossing over legal jurisdictions)
Understand the Implications of Cloud to Enterprise Risk Management
- Assess providers risk management programs (e.g., controls, methodologies, policies, risk profile, risk appetite)
- Difference between data owner/controller vs. data custodian/processor
- Regulatory transparency requirements (e.g., breach notification, Sarbanes-Oxley (SOX), General Data Protection Regulation (GDPR))
- Risk treatment (i.e., avoid, mitigate, transfer, share, acceptance)
- Different risk frameworks
- Metrics for risk management
- Assessment of risk environment (e.g., service, vendor, infrastructure, business)
Understand Outsourcing and Cloud Contract Design
- Business requirements (e.g., service-level agreement (SLA), master service agreement (MSA), statement of work (SOW))
- Vendor management (e.g., vendor assessments, vendor lock-in risks, vendor viability, escrow)
- Contract management (e.g., right to audit, metrics, definitions, termination, litigation, assurance, compliance, access to cloud/data, cyber risk insurance)
- Supply-chain management (e.g., International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 27036)
So, now we are done with the exam syllabus details. Lets now move on to the most important step for the CCSP Exam Preparation – Study guide and resources.
Preparation resources for Certified Cloud Security Professional (CCSP) Exam
The Certified Cloud Security Professional (CCSP) exam is known to be tough. It checks how much individuals know and can do in cloud security. It covers a lot of areas like cloud security design, how it works, following laws and rules, and making sure apps are secure.
To succeed in the CCSP exam, you need to know a lot about how to keep cloud systems secure and be able to use that knowledge in practical situations. The exam is in a multiple-choice format and usually lasts for about 4 hours.
For the specified syllabus, there are an infinite number of preparation resources accessible. Always keep in mind that the resources you decide to use will determine the outcome. If you select the appropriate set of resources, passing the test will be simpler. These materials can be used in conjunction with our Ultimate CCSP Exam Guide.
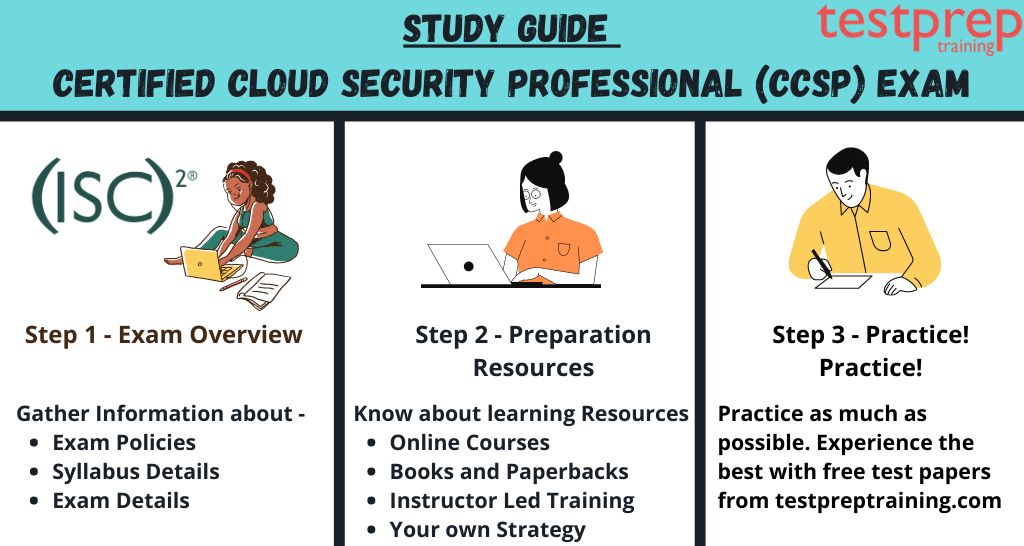
The Book Clubs
Ultimately, when we think about studying for any exam, books are the first resource that spring to mind. We have a ton of books that may be used for this particular exam. The list of books for this test is available when you search the web for information about it. Some novels are
- Firstly, Official (ISC)² Guide to the CCSP CBK, Second Edition by Adam Gordon (Editor). Publisher: Sybex. (2016)
- Secondly, CSA Security Guidance for Critical Areas of Focus in Cloud Computing v4.0. by Mogul, R., Arlen, J., Lane, A., Peterson, G., and Rothman, M. Publisher: Cloud Security Alliance. (2017)
- Thirdly, Architecting the Cloud: Design Decisions for Cloud Computing Service Models (SaaS, PaaS, and IaaS), First Edition by Michael J. Kavis. Publisher: Wiley Publishing, Inc. (2014)
- Fourthly, Cloud Security: A Comprehensive Guide to Secure Cloud Computing, First Edition by Ronald L. Krutz and Russell Dean Vines. Publisher: Wiley Publishing, Inc. (2010)
(ISC)2 Online Self-Paced Training and Official CCSP Flash Cards
(ISC)2 Online self-paced training can be used as an alternative to conventional classroom instruction. In other words, it enables applicants to use interactive study materials and study according to their own comfortable timetable. You have 120 days to access the course materials after making your payment.
Similarly to this, CCSP candidates can study whenever and wherever they want for their CCSP certification test by using Official CCSP Flash Cards. You will receive quick feedback as you take the exam on whether your response is right or not. Also, it provides the capability to mark specific cards for a different study. To make learning easier, the cards are divided into sections for each topic. Above all, this learning tool is the newest, most original, and most engaging approach to assessing your familiarity with the topic of cloud security.
Online classes and Instructor led trainings
The resources for online training are also freely available. You can pick from a wide variety of courses offered by several platforms that will give you a thorough grasp and mental clarity. They provide engaging sessions where you can simply have your questions answered. The instructor-led trainings are created by subject matter experts, which may truly aid in conceptual understanding.
Basic Terms to focus for the Exam
Here are some important terms and concepts related to the Certified Cloud Security Professional (CCSP) Exam:
- Cloud Computing: A model that offers instant access to a shared collection of computer resources like servers, storage, apps, and services through the internet.
- Cloud Service Models: There are three main types of cloud services: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
- Cloud Deployment Models: There are three main types of cloud deployment models: Public Cloud, Private Cloud, and Hybrid Cloud.
- Cloud Security: The set of policies, controls, procedures, and technologies designed to protect cloud-based assets, including data, applications, and infrastructure, from security threats.
- Cloud Data Security: The set of measures designed to protect data in cloud environments from unauthorized access, use, disclosure, modification, or destruction.
- Cloud Access Security Broker (CASB): A security technology that provides visibility and control over data and applications in cloud environments.
- Cloud Encryption: The process of turning data into a secret code that only allowed people can read.
- Cloud Key Management: The process of generating, storing, and managing encryption keys used to secure cloud-based data.
- Cloud Risk Management: The process of identifying, assessing, and mitigating risks associated with cloud environments.
- Cloud Incident Response: The process of responding to security incidents in cloud environments.
- Cloud Security Governance: The process of defining and implementing policies, procedures, and controls to ensure that cloud security risks are managed effectively.
- Cloud Compliance: The process of ensuring that cloud environments meet regulatory, legal, and contractual requirements.
Your own unique strategy
Make sure you closely adhere to your schedule and devise your own individual study plan. The only thing that will advance your preparedness is independent study. You may rectify your dumb errors and quicken your pace by doing this. You can also refer to online tutorials by Testpreptraining.com!
Blogs and Online Cloud Community
You can read blogs provided for improving your learning curve. Also, you can also ask your doubts on the cloud communities without any hesitation. Cloud communities are the group of people who have cleared the exam of similar interest. You can even form the groups with the people who have the same interest and wants to crack the same exam to pool resources and other advantages.
Practice Tests
Practice exams and test series are crucial components of the preparation process for this exam. The CCSP mock tests help in pinpointing your preparation’s weak points. When you actually take the exam, they help you feel more at ease and more confident. You should continue taking test series on a regular basis so that you can strengthen your weak areas. They improve performance evaluation and provide guidance for your preparation. There are a ton of trustworthy websites that provide you with quality practice tests and test series. Try a free practice test now!
Summarizing the Preparation Ways:
Here are some steps you can follow to help you pass the Certified Cloud Security Professional (CCSP) exam:
- Familiarize yourself with the exam content: Review the exam objectives and familiarize yourself with the topics that will be covered.
- Study the official ISC2 CCSP curriculum: The official ISC2 CCSP curriculum provides a comprehensive overview of the topics covered on the exam.
- Take a training course: Consider taking a training course that is specifically designed to prepare individuals for the CCSP exam.
- Gain practical experience: Gaining hands-on experience with cloud security technologies and practices can help you understand the concepts covered on the exam.
- Practice with mock exams: Practice with mock exams to help identify areas where you need to focus your studies.
- Join a study group: Joining a study group can help you collaborate with others who are also preparing for the exam.
- Stay updated with the latest technologies and best practices: The field of cloud security is constantly evolving, so stay updated with the latest technologies and best practices.



