When preparing for the CISSP Certified Information Systems Security Professional exam, it’s crucial to be efficient and gather all the resources you need to start preparing. In this article, you’ll find a study guide that includes expert preparation advice, learning materials, and ongoing feedback to improve your exam readiness. We’re confident that this exam guide will assist you in your journey to pass the certification exam.
Perhaps this is your first move toward the certification, or perhaps you are coming back for another round. Since you have made your mind to take the exam with an expectation to get proper guidance and expert resources, we suggest not to worry and relax. The certification exam is a stepping stone to a new high-paying job and an Astonishing career. But, before you get too excited. Let’s first begin with the study guide, it’s time for you to view all the exam details so that we don’t miss on anythjing. So, without a further due, let’s begin.
Exam Description
The CISSP, Certified Information Systems Security Professional exam, checks the extensive technical and managerial knowledge of an information security expert. It’s a widely recognized certification in the information security field. The exam assesses whether a candidate can efficiently plan, build, and oversee an organization’s overall security strategy.
Target Audience
Candidates who wish to appear for the CISSP exam must comply with the following requirements –
- Minimum of 5 years cumulative paid work experience in 2 or more of the 8 domains of the CISSP CBK.
- If a candidate doesn’t have enough experience to become a CISSP, they can become an Associate of (ISC)² by passing the CISSP exam. After that, they have 6 years to gain the necessary 5 years of experience.
Learning Objectives
The main aim of this exam is to let candidates have a clear understanding of the following tasks: the CISSP exam topics
Domain 1: Security and Risk Management 16%
1.1 – Understand, adhere to, and promote professional ethics
- ISC2 Code of Professional Ethics
- Organizational code of ethics
1.2 – Understand and apply security concepts
- Confidentiality, integrity, and availability, authenticity, and nonrepudiation (5 Pillars of Information Security)
1.3 – Evaluate and apply security governance principles
- Alignment of the security function to business strategy, goals, mission, and objectives
- Organizational processes (e.g., acquisitions, divestitures, governance committees)
- Organizational roles and responsibilities
- Security control frameworks (e.g., International Organization for Standardization (ISO), National Institute of Standards and Technology (NIST), Control Objectives for Information and Related Technology (COBIT), Sherwood Applied Business Security Architecture (SABSA), Payment Card Industry (PCI), Federal Risk and Authorization Management Program (FedRAMP))
- Due care/due diligence
1.4 – Understand legal, regulatory, and compliance issues that pertain to information security in a holistic context
- Cybercrimes and data breaches
- Licensing and Intellectual Property requirements
- Import/export controls
- Transborder data flow
- Issues related to privacy (e.g., General Data Protection Regulation (GDPR), California Consumer Privacy Act, Personal Information Protection Law, Protection of Personal Information Act)
- Contractual, legal, industry standards, and regulatory requirements
1.5 – Understand requirements for investigation types (i.e., administrative, criminal, civil, regulatory, industry standards)
1.6 – Develop, document, and implement security policy, standards, procedures, and guidelines
- Alignment of the security function to business strategy, goals, mission, and objectives
- Organizational processes (e.g., acquisitions, divestitures, governance committees)
- Organizational roles and responsibilities
- Security control frameworks (e.g., International Organization for Standardization (ISO), National Institute of Standards and Technology (NIST), Control Objectives for Information and Related Technology (COBIT), Sherwood Applied Business Security Architecture (SABSA), Payment Card Industry (PCI), Federal Risk and Authorization Management Program (FedRAMP))
- Due care/due diligence
1.7 – Identify, analyze, assess, prioritize, and implement Business Continuity (BC) requirements
- Business impact analysis (BIA)
- External dependencies
1.8 – Contribute to and enforce personnel security policies and procedures
- Candidate screening and hiring
- Employment agreements and policy driven requirements
- Onboarding, transfers, and termination processes
- Vendor, consultant, and contractor agreements and controls
1.9 – Understand and apply risk management concepts
- Threat and vulnerability identification
- Risk analysis, assessment, and scope
- Risk response and treatment (e.g., cybersecurity insurance)
- Applicable types of controls (e.g., preventive, detection, corrective)
- Control assessments (e.g., security and privacy)
- Continuous monitoring and measurement
- Reporting (e.g., internal, external)
- Continuous improvement (e.g., risk maturity modeling)
- Risk frameworks (e.g., International Organization for Standardization (ISO), National Institute of Standards and Technology (NIST), Control Objectives for Information and Related Technology (COBIT), Sherwood Applied Business Security Architecture (SABSA), Payment Card Industry (PCI))
1.10 – Understand and apply threat modeling concepts and methodologies
1.11 – Apply Supply Chain Risk Management (SCRM) concepts
- Risks associated with the acquisition of products and services from suppliers and providers (e.g., product tampering, counterfeits, implants)
- Risk mitigations (e.g., third-party assessment and monitoring, minimum security requirements, service level requirements, silicon root of trust, physically unclonable function, software bill of materials)
1.12 – Establish and maintain a security awareness, education, and training program
- Methods and techniques to increase awareness and training (e.g., social engineering, phishing, security champions, gamification)
- Periodic content reviews to include emerging technologies and trends (e.g., cryptocurrency, artificial intelligence (AI), blockchain)
- Program effectiveness evaluation
Domain 2: Asset Security 10%
2.1 Identify and classify information and assets
- Data classification
- Asset Classification
2.2 Establish information and asset handling requirements
2.3 Provision information and assets securely
- Information and asset ownership
- Asset inventory (e.g., tangible, intangible)
- Asset management
2.4 – Manage data lifecycle
- Data roles (i.e., owners, controllers, custodians, processors, users/subjects)
- Data collection
- Data location
- Data maintenance
- Data retention
- Data remanence
- Data destruction
2.5 – Ensure appropriate asset retention (e.g., End-of-Life (EOL), End-of-Support (EOS))
2.6 – Determine data security controls and compliance requirements
- Data states (e.g., in use, in transit, at rest)
- Scoping and tailoring
- Standards selection
- Data protection methods (e.g., Digital Rights Management (DRM), Data Loss Prevention (DLP), Cloud Access Security Broker (CASB))
Domain 3: Security Architecture and Engineering 13%
3.1 – Research, implement and manage engineering processes using secure design principles
- Threat modeling
- Least privilege
- Defense in depth
- Secure defaults
- Fail securely
- Separation of Duties (SoD)
- Keep it simple and small
- Zero trust or trust but verify
- Privacy by design
- Shared responsibility
- Secure access service edge
3.2 – Understand the fundamental concepts of security models (e.g., Biba, Star Model, Bell-LaPadula)
3.3 – Select controls based upon systems security requirements
3.4 – Understand security capabilities of Information Systems (IS) (e.g., memory protection, Trusted Platform Module (TPM), encryption/decryption)
3.5 – Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements
- Client-based systems
- Server-based systems
- Database systems
- Cryptographic systems
- Industrial Control Systems (ICS)
- Cloud-based systems (e.g., Software as a Service (SaaS), Infrastructure as a Service (IaaS), Platform as a Service (PaaS))
- Distributed systems
- Internet of Things (IoT)
- Microservices (e.g., application programming interface (API))
- Containerization
- Serverless
- Embedded systems
- High-Performance Computing systems
- Edge computing systems
- Virtualized systems
3.6 – Select and determine cryptographic solutions
- Cryptographic life cycle (e.g., keys, algorithm selection)
- Cryptographic methods (e.g., symmetric, asymmetric, elliptic curves, quantum)
- Public key infrastructure (PKI) (e.g., quantum key distribution
3.7 – Understand methods of cryptanalytic attacks
- Brute force
- Ciphertext only
- Known plaintext
- Frequency analysis
- Chosen ciphertext
- Implementation attacks
- Side-channel
- Fault injection
- Timing
- Man-in-the-Middle (MITM)
- Pass the hash
- Kerberos exploitation
- Ransomware
3.8 – Apply security principles to site and facility design
3.9 – Design site and facility security controls
- Wiring closets/intermediate distribution facilities
- Server rooms/data centers
- Media storage facilities
- Evidence storage
- Restricted and work area security
- Utilities and Heating, Ventilation, and Air Conditioning (HVAC)
- Environmental issues (e.g., natural disasters, man-made)
- Fire prevention, detection, and suppression
- Power (e.g., redundant, backup)
3.10 – Manage the information system lifecycle
- Stakeholders needs and requirements
- Requirements analysis
- Architectural design
- Development /implementation
- Integration
- Verification and validation
- Transition/deployment
- Operations and maintenance/sustainment
- Retirement/disposal
Domain 4: Communication and Network Security 13%
4.1 – Apply secure design principles in network architectures
- Open System Interconnection (OSI) and Transmission Control Protocol/Internet Protocol (TCP/IP) models
- Internet Protocol (IP) version 4 and 6 (IPv6) (e.g., unicast, broadcast, multicast, anycast)
- Secure protocols (e.g., Internet Protocol Security (IPSec), Secure Shell (SSH), Secure Sockets Layer (SSL)/ Transport Layer Security (TLS))
- Implications of multilayer protocols
- Converged protocols (e.g., Internet Small Computer Systems Interface (iSCSI), Voice over Internet Protocol (VoIP), InfiniBand over Ethernet, Compute Express Link)
- Transport architecture (e.g., topology, data/control/management plane, cut-through/store-and-forward)
- Performance metrics (e.g., bandwidth, latency, jitter, throughput, signal-to-noise ratio)
- Traffic flows (e.g., north-south, east-west)
- Physical segmentation (e.g., in-band, out-of-band, air-gapped)
- Logical segmentation (e.g., virtual local area networks (VLANs), virtual private networks (VPNs), virtual routing and forwarding, virtual domain)
- Micro-segmentation (e.g., network overlays/encapsulation; distributed firewalls, routers, intrusion detection system (IDS)/intrusion prevention system (IPS), zero trust)
- Edge networks (e.g., ingress/egress, peering)
- Wireless networks (e.g., Bluetooth, Wi-Fi, Zigbee, satellite)
- Cellular/mobile networks (e.g., 4G, 5G)
- Content distribution networks (CDN)
- Software defined networks (SDN), (e.g., application programming interface (API), Software-Defined Wide- Area Network, network functions virtualization)
- Virtual Private Cloud (VPC)
- Monitoring and management (e.g., network observability, traffic flow/shaping, capacity management, fault detection and handling)
4.2 – Secure network components
- Operation of infrastructure (e.g., redundant power, warranty, support)
- Transmission media (e.g., physical security of media, signal propagation quality)
- Network Access Control (NAC) systems (e.g., physical, and virtual solutions)
- Endpoint security (e.g., host-based)
4.3 – Implement secure communication channels according to design
- Voice, video, and collaboration (e.g., conferencing, Zoom rooms)
- Remote access (e.g., network administrative functions)
- Data communications (e.g., backhaul networks, satellite)
- Third-party connectivity (e.g., telecom providers, hardware support)
Domain 5: Identity and Access Management (IAM) 13%
5.1 Control physical and logical access to assets
- Information
- Systems
- Devices
- Facilities
- Application
- Services
5.2 Design identification and authentication strategy (e.g., people, devices, and services)
- Groups and Roles
- Authentication, Authorization and Accounting (AAA) (e.g., multi-factor authentication (MFA), password-less authentication)
- Session management
- Registration, proofing, and establishment of identity
- Federated Identity Management (FIM)
- Credential management systems (e.g., Password vault)
- Single sign-on (SSO)
- Just-In-Time
5.3 Federated identity with a third-party service
- On-premise
- Cloud
- Hybrid
5.4 Implement and manage authorization mechanisms
- Role Based Access Control (RBAC)
- Rule-based access control
- Mandatory Access Control (MAC)
- Discretionary Access Control (DAC)
- Attribute Based Access Control (ABAC)
- Risk based access control
- Access policy enforcement (e.g., policy decision point, policy enforcement point)
5.5 Manage the identity and access provisioning lifecycle
- Account access review (e.g., user, system, service)
- Provisioning and deprovisioning (e.g., on /off boarding and transfers)
- Role definition and transition (e.g., people assigned to new roles)
- Privilege escalation (e.g., use of sudo, auditing its use)
- Service accounts management
5.6 – Implement authentication systems
Domain 6: Security Assessment and Testing 12%
6.1 Design and validate assessment, test, and audit strategies
- Internal (e.g., within organization control)
- External (e.g., outside organization control)
- Third-party (e.g., outside of enterprise control)
- Location (e.g., on-premises, cloud, hybrid)
6.2 Conduct security control testing
- Vulnerability assessment
- Penetration testing (e.g., red, blue, and/or purple team exercises)
- Log reviews
- Synthetic transactions/benchmarks
- Code review and testing
- Misuse case testing
- Coverage analysis
- Interface testing (e.g., user interface, network interface, application programming interface (API))
- Breach attack simulations
- Compliance checks
6.3 Collect security process data (e.g., technical and administrative)
- Account management
- Management review and approval
- Key performance and risk indicators
- Backup verification data
- Training and awareness
- Disaster Recovery (DR) and Business Continuity (BC)
6.4 Analyze test output and generate report
- Remediation
- Exception handling
- Ethical disclosure
6.5 Conduct or facilitate security audits
- Internal (e.g., within organization control)
- External (e.g., outside organization control)
- Third-party (e.g., outside of enterprise control)
- Location (e.g., on-premises, cloud, hybrid)
Domain 7: Security Operations 13%
7.1 Understand and comply with investigations
- Evidence collection and handling
- Reporting and documentation
- Investigative techniques
- Digital forensics tools, tactics, and procedures
- Artifacts (e.g., data, computer, network, mobile device)
7.2 Conduct logging and monitoring activities
- Intrusion detection and prevention (IDPS)
- Security Information and Event Management (SIEM)
- Continuous monitoring and tuning
- Egress monitoring
- Log management
- Threat intelligence (e.g., threat feeds, threat hunting)
- User and Entity Behavior Analytics (UEBA)
7.3 – Perform Configuration Management (CM) (e.g., provisioning, baselining, automation)
7.4 – Apply foundational security operations concepts
- Need-to-know/least privilege
- Separation of Duties (SoD) and responsibilities
- Privileged account management
- Job rotation
- Service Level Agreements (SLAs)
7.5 – Apply resource protection
- Media management
- Media protection techniques
- Data at rest/data in transit
7.6 – Conduct incident management
- Detection
- Response
- Mitigation
- Reporting
- Recovery
- Remediation
- Lessons learned
7.7 – Operate and maintain detective and preventative measures
- Firewalls (e.g., next generation, web application, network)
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)
- Whitelisting/blacklisting
- Third-party provided security services
- Sandboxing
- Honeypots/honeynets
- Anti-malware
- Machine learning and Artificial Intelligence (AI) based tools
7.8 – Implement and support patch and vulnerability management
7.9 – Understand and participate in change management processes
7.10 – Implement recovery strategies
- Backup storage strategies (e.g., cloud storage, onsite, offsite)
- Recovery site strategies (e.g., cold vs. hot, resource capacity agreements)
- Multiple processing sites
- System resilience, high availability (HA), Quality of Service (QoS), and fault tolerance
7.11 – Implement Disaster Recovery (DR) processes
- Response
- Personnel
- Communications (e.g., methods)
- Assessment
- Restoration
- Training and awareness
- Lessons learned
7.12 – Test Disaster Recovery Plans (DRP)
- Read-through/tabletop
- Walkthrough
- Simulation
- Parallel
- Full interruption
- Communications (e.g., methods)
7.13 – Participate in Business Continuity (BC) planning and exercises
7.14 – Implement and manage physical security
- Perimeter security controls
- Internal security controls
7.15 – Address personnel safety and security concerns
- Travel
- Security training and awareness (e.g., insider threat, social media impacts, two-factor authentication (2FA) fatigue)
- Emergency management
- Duress
Domain 8: Software Development Security 10%
8.1 Understand and integrate security in the Software Development Life Cycle (SDLC)
- Development methodologies (e.g., Agile, Waterfall, DevOps, DevSecOps, Scaled Agile Framework)
- Maturity models (e.g., Capability Maturity Model (CMM), Software Assurance Maturity Model (SAMM))
- Operation and maintenance
- Change management
- Integrated Product Team
8.2 Identify and apply security controls in software development ecosystems
- Programming languages
- Libraries
- Tool sets
- Integrated Development Environment (IDE)
- Runtime
- Continuous Integration and Continuous Delivery (CI/CD)
- Security Orchestration, Automation, and Response (SOAR)
- Software Configuration Management (SCM)
- Code repositories
- Application security testing (e.g., static application security testing (SAST), dynamic application security testing (DAST), software composition analysis, Interactive Application Security Test (IAST))
8.3 Assess the effectiveness of software security
- Auditing and logging of changes
- Risk analysis and mitigation
8.4 Assess security impact of acquired software
- Commercial-off-the-shelf (COTS)
- Open source
- Third-party
- Managed services (e.g., enterprise applications)
- Cloud services (e.g., Software as a Service (SaaS), Infrastructure as a Service (IaaS), Platform as a Service (PaaS))
8.5 Define and apply secure coding guidelines and standards
- Security weaknesses and vulnerabilities at the source-code level
- Security of Application Programming Interfaces (APIs)
- Secure coding practices
- Software-defined security
This brings us to the end of all the CISSP exam details. However, if you wish to dive in for a deeper understanding of each and every domain and topics, you visit the tutorial page for CISSP, Certified Information Systems Security Professional exam here!
Comprehensive Study Guide for Certified Information Systems Security Professional (CISSP) Exam
Every exam and certification has its own set of rules. If you’re serious about this, be sure to carefully check the CISSP exam requirements. It’s frustrating to spend months studying for an exam you can’t even take or pass an exam that doesn’t lead to certification! Also, preparing for the CISSP exam is no easy task. Our simple CISSP exam study guide is made to help you locate the right information and offer you practice papers for free.
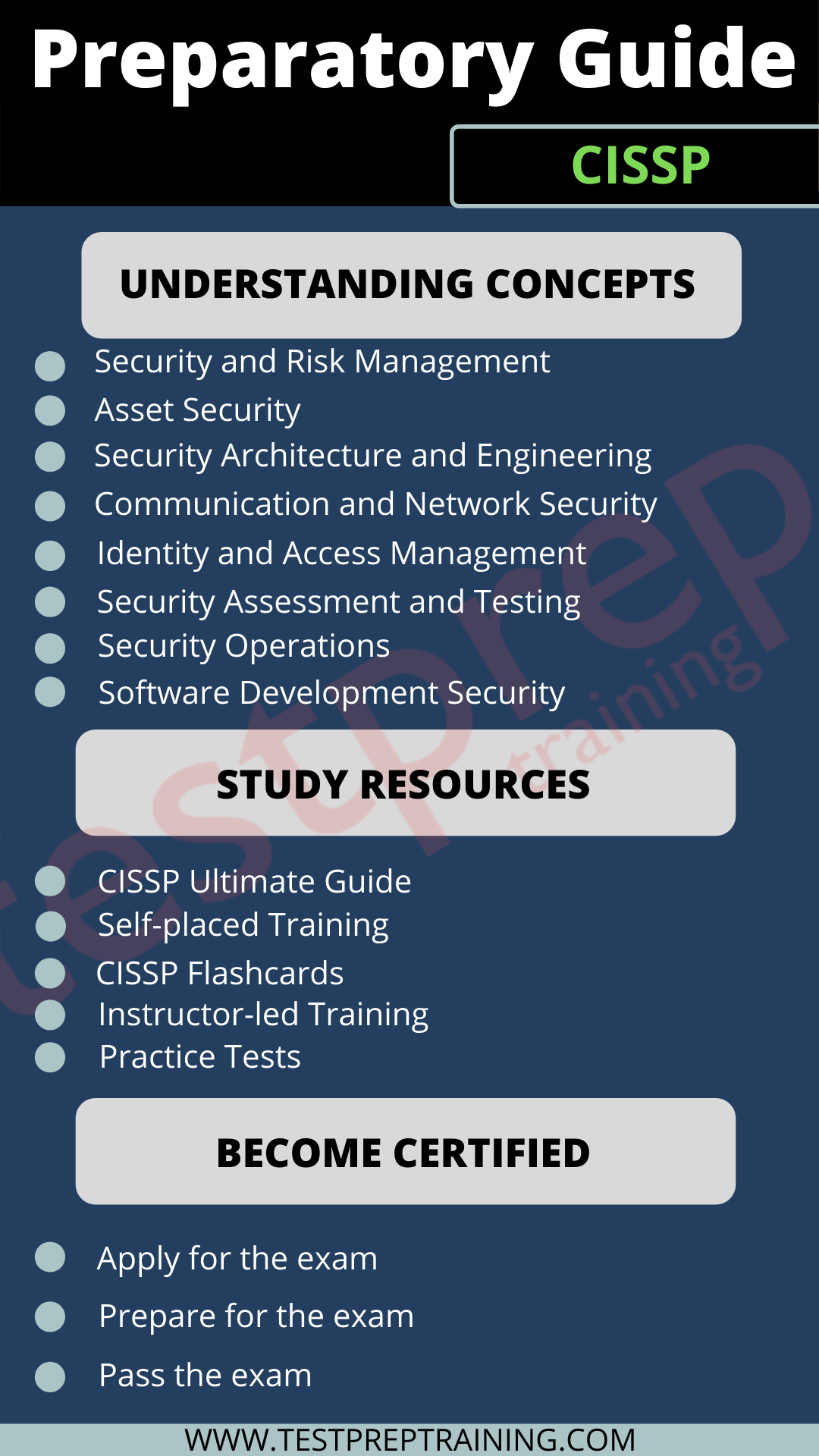
CISSP Ultimate Guide
The CISSP Ultimate Guide is your go-to place for all your questions about the CISSP exam. It’s like a complete package that covers everything about the CISSP exam and the topics it includes. If you want a thorough review of the information, you should check out this guide and save it so you can access it whenever you need, wherever you are.
Self-placed Training
(ISC)² Online Self-Paced Training is an alternative to traditional training classroom. These modern and exclusive training courses allow candidates to study on their own convenient schedule with interactive study material. Remember, once you purchase the course, you can access the course content for a period of 120 days.
CISPP Flashcards
Candidates preparing for the CISSP exam can now study anytime and anywhere for the certification exam. Yes, you heard it right. CISSP Flashcards provided by (ISC)² helps candidates get immediate feedback relating to their queries. Also, these flashcards provide the ability to flag individual cards for a separate study. The cards are sectioned for each domain to make learning easier and efficient.
Instructor-led Training
In the world of the internet, nothing is as difficult as it used to be. The same goes for the training process. Since, training is not feasible for everyone, (ISC)² offers instructor-led training as an option to help candidates prepare for the exam. These online training sessions allow you to participate from the convenience of your computer, thereby saving you travel time and expense.
Practice Tests
Practice tests play a pivotal role during your exam preparation. They not only help you find out your strengths but also direct you to master your possible weak areas. The evolution of practice tests has done nothing but added more to its generosity. They are considered as one of the most efficient sources to study for the exam as they offer live CISSP exam experience. Therefore, try as many practice tests as much as you can.