One of the most pressing challenges facing the IT industry today is a shortage of skilled professionals who can effectively manage and secure an IT team. Amazon Web Services has taken steps to address this issue by introducing the AWS Security certification, which validates the knowledge of skilled cloud security professionals in securing the AWS platform. Passing the AWS Certified Security Specialty exam requires significant effort and dedication due to its specialist level of difficulty. However, to succeed in this certification, candidates must obtain the right preparation materials. At TestprepTraining, we offer the AWS Certified Security Specialty Online Course, developed by subject matter experts, to help individuals gain the necessary proficiency.
The AWS Certified Security Specialty SCS-C01 Certification Online Course is designed to provide learners with expert learning resources to accelerate their careers in cloud security. Achieving this AWS security certification demonstrates one’s expertise and domain specialization in working with cloud security. Before delving into the online course, it is important to review some essential details about the exam.
About AWS Certified Security-Specialty Exam
In terms of specialization, the AWS Certified Security-Specialty certification is exactly where you need to improve your learning curve. Candidates must design and implement security solutions as well as direct secure AWS workloads. Anyone interested in securing assets on Amazon Web Services can apply for AWS Security Specialty Certification. The AWS certification exam you need to take can be compared with other certifications at the specialist level offered by Amazon. With an AWS Certified Security Specialist Certification on your CV, you are one step ahead of your peers in taking up lucrative AWS opportunities. With the evolving technology, the demands for certification by AWS Certified Security Specialist (AWS CSS) seems to be extremely high. Saying so, it improves career opportunities and tends to increase your confidence in the fact that they are certified in their respective fields of expertise.
Exam Overview
The AWS Security Specialty Certification is not an advanced-level exam, and the questions reflect the difficulty of fully testing the holistic knowledge of an AWS security expert. The AWS Certified Security – Specialty (SCS-C01) examination will help you validate your ability to show your proficiency in securing the AWS platform by validating your understanding about: –
- Specialized data distributions and AWS data security mechanisms.
- Also, data-encryption techniques and AWS mechanisms to enforce them.
- Secure Internet protocols and AWS tools to achieve them.
- Subsequently, skills gained from two or more years of production deployment experience using the services of AWS Security.
- Finally, your intelligence to make agreement decisions regarding cost, surveillance, and deployment complexity.
This marks an opportunity for professionals to validate their knowledge and skills in the AWS Certified Security Specialist certification exam. AWS accreditation doesn’t simply look great on your resume. But it can altogether support your dream of getting a salary hike. As per independent surveys, 70% of AWS experts announced a compensation increment of up to 20% subsequent attaining the certification.
Recommended Knowledge
This learning way is ideal for anybody keen on figuring out how to comprehend, clarify, and execute keys to authorize security controls over all degrees of AWS infrastructure arrangements. The Exam material is tested to reflect your experience as an AWS-certified safety specialist as well as your skills and knowledge in your field, as in any question.
Before you plan to sit for the exam, keep in check the following AWS certified security – specialty prerequisites:
- At least 5 years of IT security experience, structuring, and actualizing security arrangements.
- In any event 2 years of hands-on experience securing AWS Workloads.
- Knowledge about various security conventions for handling workloads on AWS.
Exam Details
AWS Security Specialty Certification questions have been designed in 65 MCQ questions to give you a tough fight for 170 minutes, in selecting the right response. AWS treats every answered question as an incorrect response, and there is no negative marking, unlike other competitive exams. Finally, you will get the results of your examination as a score from 100–1,000, with a minimum passing bar to get 750 marks. Your total score will be scaled among different types of questions to get a detailed report about your performance.
| Name of the exam | AWS Certified Security – Specialty |
| Exam code | SCS-C01 |
| No. of questions asked | 65 |
| Passing marks | 750/1000 |
| Cost of taking the exam | $300 USD |
| Languages available | English and Japanese, Korean, Simplified Chinese |
| Exam validity | 3 years |
| Exam format | Multiple choice and multiple response |
Course Outline
The AWS Certified Security Specialty course outline has been divided into five domains, which include the following domains. Going through each of the domains will guide you with the learning concepts required to pass the examination.
Domain 1: Threat Detection and Incident Response (14%)
Task Statement 1.1: Design and implement an incident response plan.
Knowledge of:
- AWS best practices for incident response (AWS Documentation: AWS Security Incident Response Guide)
- Cloud incidents
- Roles and responsibilities in the incident response plan (AWS Documentation: Define roles and responsibilities)
- AWS Security Finding Format (ASFF) (AWS Documentation: AWS Security Finding Format (ASFF))
Skills in:
- Implementing credential invalidation and rotation strategies in response to compromises (for example, by using AWS Identity and Access Management [IAM] and AWS Secrets Manager) (AWS Documentation: Automatically rotate IAM user access keys at scale with AWS Organizations and AWS Secrets Manager)
- Isolating AWS resources (AWS Documentation: Design isolated resource environments)
- Designing and implementing playbooks and runbooks for responses to security incidents (AWS Documentation: Develop and test security incident response playbooks)
- Deploying security services (for example, AWS Security Hub, Amazon Macie, Amazon GuardDuty, Amazon Inspector, AWS Config, Amazon Detective, AWS Identity and Access Management Access Analyzer) (AWS Documentation: Security, identity, and compliance)
- Configuring integrations with native AWS services and third-party services (for example, by using Amazon EventBridge and the ASFF)
Task Statement 1.2: Detect security threats and anomalies by using AWS services.
Knowledge of:
- AWS managed security services that detect threats (AWS Documentation: Monitoring data security with managed AWS security services)
- Anomaly and correlation techniques to join data across services (AWS Documentation: Concepts for anomaly or outlier detection)
- Visualizations to identify anomalies
- Strategies to centralize security findings (AWS Documentation: Centralized Security Management)
Skills in:
- Evaluating findings from security services (for example, GuardDuty, Security Hub, Macie, AWS Config, IAM Access Analyzer) (AWS Documentation: AWS service integrations with AWS Security Hub)
- Searching and correlating security threats across AWS services (for example, by using Detective)
- Performing queries to validate security events (for example, by using Amazon Athena) (AWS Documentation: Querying AWS CloudTrail logs)
- Creating metric filters and dashboards to detect anomalous activity (for example, by using Amazon CloudWatch) (AWS Documentation: Using CloudWatch anomaly detection)
Task Statement 1.3: Respond to compromised resources and workloads.
Knowledge of:
- AWS Security Incident Response Guide (AWS Documentation: AWS Security Incident Response Guide)
- Resource isolation mechanisms (AWS Documentation: Design isolated resource environments)
- Techniques for root cause analysis (AWS Documentation: What is Root Cause Analysis (RCA)?)
- Data capture mechanisms (AWS Documentation: Capture data)
- Log analysis for event validation (AWS Documentation: Analyzing log data with CloudWatch Logs Insights)
Skills in:
- Automating remediation by using AWS services (for example, AWS Lambda, AWS Step Functions, EventBridge, AWS Systems Manager runbooks, Security Hub, AWS Config) (AWS Documentation: AWS Systems Manager Automation)
- Responding to compromised resources (for example, by isolating Amazon EC2 instances) (AWS Documentation: Remediating a potentially compromised Amazon EC2 instance)
- Investigating and analyzing to conduct root cause analysis (for example, by using Detective) (AWS Documentation: What is Amazon Detective?)
- Capturing relevant forensics data from a compromised resource (for example, Amazon Elastic Block Store [Amazon EBS] volume snapshots, memory dump) (AWS Documentation: Amazon EBS snapshots)
- Querying logs in Amazon S3 for contextual information related to security events (for example, by using Athena) (AWS Documentation: Querying AWS CloudTrail logs)
- Protecting and preserving forensic artifacts (for example, by using S3 Object Lock, isolated forensic accounts, S3 Lifecycle, and S3 replication) (AWS Documentation: Using S3 Object Lock)
- Preparing services for incidents and recovering services after incidents (AWS Documentation: Recovery)
Domain 2: Security Logging and Monitoring (18%)
Task Statement 2.1: Design and implement monitoring and alerting to address security events.
Knowledge of:
- AWS services that monitor events and provide alarms (for example, CloudWatch, EventBridge) (AWS Documentation: Alarm events and EventBridge)
- AWS services that automate alerting (for example, Lambda, Amazon Simple Notification Service [Amazon SNS], Security Hub) (AWS Documentation: Automated response and remediation)
- Tools that monitor metrics and baselines (for example, GuardDuty, Systems Manager)
Skills in:
- Analyzing architectures to identify monitoring requirements and sources of data for security monitoring (AWS Documentation: Designing and implementing logging and monitoring with Amazon CloudWatch)
- Analyzing environments and workloads to determine monitoring requirements (AWS Documentation: Perform an analysis on the workload demand)
- Designing environment monitoring and workload monitoring based on business and security requirements
- Setting up automated tools and scripts to perform regular audits (for example, by creating custom insights in Security Hub) (AWS Documentation: Custom insights)
- Defining the metrics and thresholds that generate alerts (AWS Documentation: Using Amazon CloudWatch alarms)
Task Statement 2.2: Troubleshoot security monitoring and alerting.
Knowledge of:
- Configuration of monitoring services (for example, Security Hub) (AWS Documentation: What is AWS Security Hub?)
- Relevant data that indicates security events (AWS Documentation: Logging and events)
Skills in:
- Analyzing the service functionality, permissions, and configuration of resources after an event that did not provide visibility or alerting (AWS Documentation: Refining permissions in AWS using last accessed information)
- Analyzing and remediating the configuration of a custom application that is not reporting its statistics (AWS Documentation: What Is AWS Config?)
- Evaluating logging and monitoring services for alignment with security requirements (AWS Documentation: Monitoring and Logging)
Task Statement 2.3: Design and implement a logging solution.
Knowledge of:
- AWS services and features that provide logging capabilities (for example, VPC Flow Logs, DNS logs, AWS CloudTrail, Amazon CloudWatch Logs) (AWS Documentation: Logging IP traffic using VPC Flow Logs)
- Attributes of logging capabilities (for example, log levels, type, verbosity) (AWS Documentation: AWS Lambda function logging in Python)
- Log destinations and lifecycle management (for example, retention period) (AWS Documentation: Managing your storage lifecycle)
Skills in:
- Configuring logging for services and applications (AWS Documentation: Configure service and application logging)
- Identifying logging requirements and sources for log ingestion
- Implementing log storage and lifecycle management according to AWS best practices and organizational requirements (AWS Documentation: Managing your storage lifecycle)
Task Statement 2.4: Troubleshoot logging solutions.
Knowledge of:
- Capabilities and use cases of AWS services that provide data sources (for example, log level, type, verbosity, cadence, timeliness, immutability) (AWS Documentation: AWS services for logging and monitoring)
- AWS services and features that provide logging capabilities (for example, VPC Flow Logs, DNS logs, CloudTrail, CloudWatch Logs) (AWS Documentation: Logging IP traffic using VPC Flow Logs)
- Access permissions that are necessary for logging (AWS Documentation: CloudWatch Logs permissions reference)
Skills in:
- Identifying misconfiguration and determining remediation steps for absent access permissions that are necessary for logging (for example, by managing read/write permissions, S3 bucket permissions, public access, and integrity) (AWS Documentation: Enabling Amazon S3 server access logging)
- Determining the cause of missing logs and performing remediation steps (AWS Documentation: Remediating security issues discovered by GuardDuty)
Task Statement 2.5: Design a log analysis solution.
Knowledge of:
- Services and tools to analyze captured logs (for example, Athena, CloudWatch Logs filter) (AWS Documentation: Logging and monitoring in Athena)
- Log analysis features of AWS services (for example, CloudWatch Logs Insights, CloudTrail Insights, Security Hub insights) (AWS Documentation: Analyzing log data with CloudWatch Logs Insights)
- Log format and components (for example, CloudTrail logs) (AWS Documentation: CloudTrail log file examples)
Skills in:
- Identifying patterns in logs to indicate anomalies and known threats (AWS Documentation: Log anomaly detection)
- Normalizing, parsing, and correlating logs (AWS Documentation: Parsing logs and structured logging)
Domain 3: Infrastructure Security (20%)
Task Statement 3.1: Design and implement security controls for edge services.
Knowledge of:
- Security features on edge services (for example, AWS WAF, load balancers, Amazon Route 53, Amazon CloudFront, AWS Shield) (AWS Documentation: How AWS WAF works with Amazon CloudFront features)
- Common attacks, threats, and exploits (for example, Open Web Application Security Project [OWASP] Top 10, DDoS)
- Layered web application architecture (AWS Documentation: Three-tier architecture overview)
Skills in:
- Defining edge security strategies for common use cases (for example, public website, serverless app, mobile app backend) (AWS Documentation: Identity and access management)
- Selecting appropriate edge services based on anticipated threats and attacks (for example, OWASP Top 10, DDoS)
- Selecting appropriate protections based on anticipated vulnerabilities and risks (for example, vulnerable software, applications, libraries) (AWS Documentation: Vulnerability Reporting)
- Defining layers of defense by combining edge security services (for example, CloudFront with AWS WAF and load balancers)
- Applying restrictions at the edge based on various criteria (for example, geography, geolocation, rate limit) (AWS Documentation: Restricting the geographic distribution of your content)
- Activating logs, metrics, and monitoring around edge services to indicate attacks (AWS Documentation: Metrics and alarms)
Task Statement 3.2: Design and implement network security controls.
Knowledge of:
- VPC security mechanisms (for example, security groups, network ACLs, AWS Network Firewall) (AWS Documentation: Security best practices for your VPC)
- Inter-VPC connectivity (for example, AWS Transit Gateway, VPC endpoints) (AWS Documentation: Amazon VPC-to-Amazon VPC connectivity options)
- Security telemetry sources (for example, Traffic Mirroring, VPC Flow Logs) (AWS Documentation: Logging IP traffic using VPC Flow Logs)
- VPN technology, terminology, and usage (AWS Documentation: What is AWS Site-to-Site VPN?)
- On-premises connectivity options (for example, AWS VPN, AWS Direct Connect) (AWS Documentation: AWS Direct Connect)
Skills in:
- Implementing network segmentation based on security requirements (for example, public subnets, private subnets, sensitive VPCs, on-premises connectivity)
- Designing network controls to permit or prevent network traffic as required (for example, by using security groups, network ACLs, and Network Firewall) (AWS Documentation: Control traffic to subnets using network ACLs)
- Designing network flows to keep data off the public internet (for example, by using Transit Gateway, VPC endpoints, and Lambda in VPCs) (AWS Documentation: What is a transit gateway?)
- Determining which telemetry sources to monitor based on network design, threats, and attacks (for example, load balancer logs, VPC Flow Logs, Traffic Mirroring) (AWS Documentation: Monitor your Network Load Balancers)
- Determining redundancy and security workload requirements for communication between on-premises environments and the AWS Cloud (for example, by using AWS VPN, AWS VPN over Direct Connect, and MACsec) (AWS Documentation: AWS Direct Connect)
- Identifying and removing unnecessary network access (AWS Documentation: Security best practices in IAM)
- Managing network configurations as requirements change (for example, by using AWS Firewall Manager) (AWS Documentation: Working with AWS Firewall Manager policies)
Task Statement 3.3: Design and implement security controls for compute workloads.
Knowledge of:
- Provisioning and maintenance of EC2 instances (for example, patching, inspecting, creation of snapshots and AMIs, use of EC2 Image Builder) (AWS Documentation: What is EC2 Image Builder?)
- IAM instance roles and IAM service roles (AWS Documentation: IAM roles)
- Services that scan for vulnerabilities in compute workloads (for example, Amazon Inspector, Amazon Elastic Container Registry [Amazon ECR]) (AWS Documentation: Scanning Amazon ECR container images with Amazon Inspector)
- Host-based security (for example, firewalls, hardening)
Skills in:
- Creating hardened EC2 AMIs (AWS Documentation: Create a custom Windows AMI)
- Applying instance roles and service roles as appropriate to authorize compute workloads (AWS Documentation: IAM roles for Amazon EC2)
- Scanning EC2 instances and container images for known vulnerabilities (AWS Documentation: Scanning Amazon EC2 instances with Amazon Inspector)
- Applying patches across a fleet of EC2 instances or container images (AWS Documentation: AWS Systems Manager Patch Manager)
- Activating host-based security mechanisms (for example, host-based firewalls)
- Analyzing Amazon Inspector findings and determining appropriate mitigation techniques (AWS Documentation: Understanding findings in Amazon Inspector)
- Passing secrets and credentials securely to compute workloads (AWS Documentation: AWS security credentials)
Task Statement 3.4: Troubleshoot network security.
Knowledge of:
- How to analyze reachability (for example, by using VPC Reachability Analyzer and Amazon Inspector) (AWS Documentation: Getting started with Reachability Analyzer)
- Fundamental TCP/IP networking concepts (for example, UDP compared with TCP, ports, Open Systems Interconnection [OSI] model, network operating system utilities)
- How to read relevant log sources (for example, Route 53 logs, AWS WAF logs, VPC Flow Logs) (AWS Documentation: Logging IP traffic using VPC Flow Logs)
Skills in:
- Identifying, interpreting, and prioritizing problems in network connectivity (for example, by using Amazon Inspector Network Reachability) (AWS Documentation: Network Reachability)
- Determining solutions to produce desired network behavior (AWS Documentation: AWS Config Managed Rules)
- Analyzing log sources to identify problems (AWS Documentation: Analyzing log data with CloudWatch Logs Insights)
- Capturing traffic samples for problem analysis (for example, by using Traffic Mirroring) (AWS Documentation: What is Traffic Mirroring?)
Domain 4: Identity and Access Management (16%)
Task Statement 4.1: Design, implement, and troubleshoot authentication for AWS resources.
Knowledge of:
- Methods and services for creating and managing identities (for example, federation, identity providers, AWS IAM Identity Center [AWS Single Sign-On], Amazon Cognito) (AWS Documentation: Identity providers and federation)
- Long-term and temporary credentialing mechanisms (AWS Documentation: Use temporary credentials)
- How to troubleshoot authentication issues (for example, by using CloudTrail, IAM Access Advisor, and IAM policy simulator) (AWS Documentation: Troubleshooting AWS CloudTrail identity and access)
Skills in:
- Establishing identity through an authentication system, based on requirements (AWS Documentation: How IAM works)
- Setting up multi-factor authentication (MFA) (AWS Documentation: General steps for enabling MFA devices)
- Determining when to use AWS Security Token Service (AWS STS) to issue temporary credentials (AWS Documentation: Requesting temporary security credentials)
Task Statement 4.2: Design, implement, and troubleshoot authorization for AWS resources.
Knowledge of:
- Different IAM policies (for example, managed policies, inline policies, identity-based policies, resource-based policies, session control policies) (AWS Documentation: Policies and permissions in IAM)
- Components and impact of a policy (for example, Principal, Action, Resource, Condition) (AWS Documentation: IAM JSON policy elements reference)
- How to troubleshoot authorization issues (for example, by using CloudTrail, IAM Access Advisor, and IAM policy simulator) (AWS Documentation: Troubleshooting AWS CloudTrail identity and access)
Skills in:
- Constructing attribute-based access control (ABAC) and role-based access control (RBAC) strategies (AWS Documentation: What is ABAC for AWS?)
- Evaluating IAM policy types for given requirements and workloads (AWS Documentation: Policy evaluation logic)
- Interpreting an IAM policy’s effect on environments and workloads (AWS Documentation: IAM policy elements: Variables and tags)
- Applying the principle of least privilege across an environment
- Enforcing proper separation of duties
- Analyzing access or authorization errors to determine cause or effect (AWS Documentation: Using AWS Identity and Access Management Access Analyzer)
- Investigating unintended permissions, authorization, or privileges granted to a resource, service, or entity (AWS Documentation: Managing access permissions for your AWS organization)
Domain 5: Data Protection (18%)
Task Statement 5.1: Design and implement controls that provide confidentiality and integrity for data in transit.
Knowledge of:
- TLS concepts (AWS Documentation: Transport Layer Security (TLS))
- VPN concepts (for example, IPsec) (AWS Documentation: What is a VPN (Virtual Private Network)?)
- Secure remote access methods (for example, SSH, RDP over Systems Manager Session Manager) (AWS Documentation: AWS Systems Manager Session Manager)
- Systems Manager Session Manager concepts
- How TLS certificates work with various network services and resources (for example, CloudFront, load balancers) (AWS Documentation: TLS listeners for your Network Load Balancer)
Skills in:
- Designing secure connectivity between AWS and on-premises networks (for example, by using Direct Connect and VPN gateways) (AWS Documentation: AWS Direct Connect )
- Designing mechanisms to require encryption when connecting to resources (for example, Amazon RDS, Amazon Redshift, CloudFront, Amazon S3, Amazon DynamoDB, load balancers, Amazon Elastic File System [Amazon EFS], Amazon API Gateway) (AWS Documentation: Encrypting Amazon RDS resources)
- Requiring TLS for AWS API calls (for example, with Amazon S3) (AWS Documentation: Infrastructure security in Amazon S3)
- Designing mechanisms to forward traffic over secure connections (for example, by using Systems Manager and EC2 Instance Connect) (AWS Documentation: Connect using EC2 Instance Connect)
- Designing cross-Region networking by using private VIFs and public VIFs
Task Statement 5.2: Design and implement controls that provide confidentiality and integrity for data at rest.
Knowledge of:
- Encryption technique selection (for example, client-side, server-side, symmetric, asymmetric) (AWS Documentation: AWS KMS concepts)
- Integrity-checking techniques (for example, hashing algorithms, digital signatures) (AWS Documentation: Checking object integrity)
- Resource policies (for example, for DynamoDB, Amazon S3, and AWS Key Management Service [AWS KMS]) (AWS Documentation: Key policies in AWS KMS)
- IAM roles and policies (AWS Documentation: Policies and permissions in IAM)
Skills in:
- Designing resource policies to restrict access to authorized users (for example, S3 bucket policies, DynamoDB policies) (AWS Documentation: Examples of Amazon S3 bucket policies)
- Designing mechanisms to prevent unauthorized public access (for example, S3 Block Public Access, prevention of public snapshots and public AMIs) (AWS Documentation: Blocking public access to your Amazon S3 storage)
- Configuring services to activate encryption of data at rest (for example, Amazon S3, Amazon RDS, DynamoDB, Amazon Simple Queue Service [Amazon SQS], Amazon EBS, Amazon EFS) (AWS Documentation: Encryption at rest in Amazon SQS)
- Designing mechanisms to protect data integrity by preventing modifications (for example, by using S3 Object Lock, KMS key policies, S3 Glacier Vault Lock, and AWS Backup Vault Lock) (AWS Documentation: Using S3 Object Lock)
- Designing encryption at rest by using AWS CloudHSM for relationaldatabases (for example, Amazon RDS, RDS Custom, databases on EC2 instances)
- Choosing encryption techniques based on business requirements (AWS Documentation: Creating an enterprise encryption strategy for data at rest)
Task Statement 5.3: Design and implement controls to manage the lifecycle of data at rest.
Knowledge of:
- Lifecycle policies
- Data retention standards
Skills in:
- Designing S3 Lifecycle mechanisms to retain data for required retention periods (for example, S3 Object Lock, S3 Glacier Vault Lock, S3 Lifecycle policy) (AWS Documentation: Managing your storage lifecycle)
- Designing automatic lifecycle management for AWS services and resources (for example, Amazon S3, EBS volume snapshots, RDS volume snapshots, AMIs, container images, CloudWatch log groups, Amazon Data Lifecycle Manager) (AWS Documentation: Amazon Data Lifecycle Manager)
- Establishing schedules and retention for AWS Backup across AWS services (AWS Documentation: Creating a backup plan)
Task Statement 5.4: Design and implement controls to protect credentials, secrets, and cryptographic key materials.
Knowledge of:
- Secrets Manager (AWS Documentation: What is AWS Secrets Manager?)
- Systems Manager Parameter Store (AWS Documentation: AWS Systems Manager Parameter Store)
- Usage and management of symmetric keys and asymmetric keys (for example, AWS KMS)
Skills in:
- Designing management and rotation of secrets for workloads (for example, database access credentials, API keys, IAM access keys, AWS KMS customer managed keys)
- Designing KMS key policies to limit key usage to authorized users (AWS Documentation: Key policies in AWS KMS)
- Establishing mechanisms to import and remove customer-provided key material (AWS Documentation: Importing key material for AWS KMS keys)
Domain 6: Management and Security Governance (14%)
Task Statement 6.1: Develop a strategy to centrally deploy and manage AWS accounts.
Knowledge of:
- Multi-account strategies (AWS Documentation: Organizing Your AWS Environment Using Multiple Accounts)
- Managed services that allow delegated administration (AWS Documentation: AWS services that you can use with AWS Organizations)
- Policy-defined guardrails
- Root account best practices (AWS Documentation: Root user best practices for your AWS account)
- Cross-account roles (AWS Documentation: Delegate access across AWS accounts using IAM roles)
Skills in:
- Deploying and configuring AWS Organizations (AWS Documentation: Creating and configuring an organization)
- Determining when and how to deploy AWS Control Tower (for example, which services must be deactivated for successful deployment) (AWS Documentation: Deploying AWS Control Tower in an AWS Landing Zone organization)
- Implementing SCPs as a technical solution to enforce a policy (for example, limitations on the use of a root account, implementation of controls in AWS Control Tower)
- Centrally managing security services and aggregating findings (for example, by using delegated administration and AWS Config aggregators) (AWS Documentation: How central configuration works)
- Securing AWS account root user credentials (AWS Documentation: AWS security credentials)
Task Statement 6.2: Implement a secure and consistent deployment strategy for cloud resources.
Knowledge of:
- Deployment best practices with infrastructure as code (IaC) (for example, AWS CloudFormation template hardening and drift detection) (AWS Documentation: AWS CloudFormation best practices)
- Best practices for tagging (AWS Documentation: Best Practices for Tagging AWS Resources)
- Centralized management, deployment, and versioning of AWS services
- Visibility and control over AWS infrastructure
Skills in:
- Using CloudFormation to deploy cloud resources consistently and securely (AWS Documentation: AWS CloudFormation best practices)
- Implementing and enforcing multi-account tagging strategies (AWS Documentation: Implementing and enforcing tagging)
- Configuring and deploying portfolios of approved AWS services (for example, by using AWS Service Catalog) (AWS Documentation: Automate AWS Service Catalog portfolio and product deployment by using AWS CDK)
- Organizing AWS resources into different groups for management (AWS Documentation: What are resource groups?)
- Deploying Firewall Manager to enforce policies (AWS Documentation: Working with AWS Firewall Manager policies)
- Securely sharing resources across AWS accounts (for example, by using AWS Resource Access Manager [AWS RAM]) (AWS Documentation: Shareable AWS resources)
Task Statement 6.3: Evaluate the compliance of AWS resources.
Knowledge of:
- Data classification by using AWS services (AWS Documentation: Data classification overview)
- How to assess, audit, and evaluate the configurations of AWS resources (for example, by using AWS Config) (AWS Documentation: Evaluating Resources with AWS Config Rules)
Skills in:
- Identifying sensitive data by using Macie (AWS Documentation: Discovering sensitive data with Amazon Macie)
- Creating AWS Config rules for detection of noncompliant AWS resources (AWS Documentation: Remediating Noncompliant Resources with AWS Config Rules)
- Collecting and organizing evidence by using Security Hub and AWS Audit Manager (AWS Documentation: Reviewing the evidence in an assessment)
Task Statement 6.4: Identify security gaps through architectural reviews and cost analysis.
Knowledge of:
- AWS cost and usage for anomaly identification (AWS Documentation: Getting started with AWS Cost Anomaly Detection)
- Strategies to reduce attack surfaces (AWS Documentation: Attack surface reduction)
- AWS Well-Architected Framework (AWS Documentation: AWS Well-Architected Framework)
Skills in:
- Identifying anomalies based on resource utilization and trends (AWS Documentation: Using CloudWatch anomaly detection)
- Identifying unused resources by using AWS services and tools (for example, AWS Trusted Advisor, AWS Cost Explorer) (AWS Documentation: Analyzing your costs with AWS Cost Explorer)
- Using the AWS Well-Architected Tool to identify security gaps (AWS Documentation: Security in AWS Well-Architected Tool)
AWS Certified Security Specialty Online Course
To help you in capturing the AWS Certified Security Specialty and to make sure you don’t have to fall back on something – you can take a look at our AWS Certified Security Specialty Online Course. Our learning course will take you through the various security services alongside the distinctive security features accessible through different AWS services.
- Our course starts with a prologue to the most well-known security administration that is accessible, Identity, and Access Management (IAM). During the initial courses and labs, it gives an overview of the Access Management and Identities, both inside and remotely, covering diverse verification and authorization methods.
- Next, it presents various AWS Security Administrations related to auditing and agreement. Some of them have their foundation basis on Machine Learning – For example, Amazon Guard Duty and Amazon Macie.
- We will also take a look into Monitoring and logging to help you examine different AWS services to monitor and trace log data. And also use it as a medium to find vulnerabilities. Adding to this, we have included several courses and labs to look into Encryption, and Data Protection using different encryption mechanisms across a range of AWS services.
- Next, we have Application and Network security, diving in to look at various services and procedures that can be executed. This is to help you shield your Web Apps along with your VPC infrastructure, from both intrinsic and extrinsic threats.
Key Components – AWS Certified Security Specialty Online Course
Let us have a quick overview of the key components we focus in the AWS Certified Security Specialty Online Course –
- Identity and Access Management
- Detective Controls
- Infrastructure Protection
- Data Protection
- Incident Response
Now it is time to dig deeper into the technical aspects of the online course. Taking the online course will help you gain an in-depth understanding of every concept and practice involved in attaining the certification, and becoming an AWS Certified Security Specialist.
Online Course Module – AWS Security Specialty Exam
Start your AWS Certified Security Specialty preparation with an online course and targeted training program. This online course material helps you gain extra knowledge and skills to get ready for the certification exam. The AWS Certified Security Specialty Online Course is all about making sure applications are secure in AWS. This certification is one of three Specialty certifications offered by AWS.
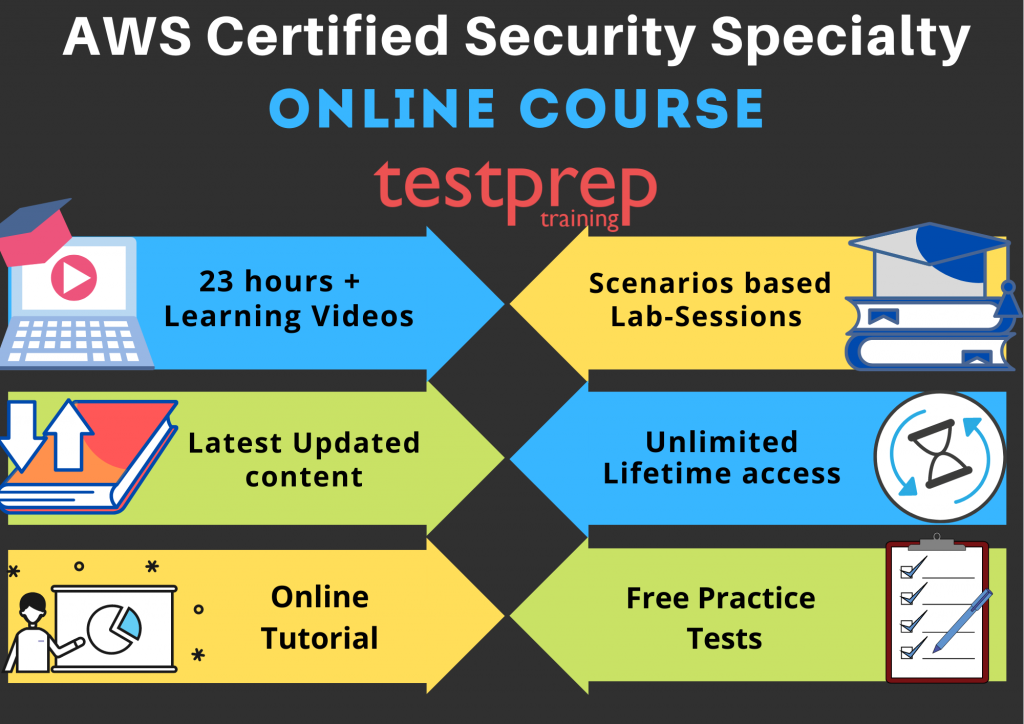
What’s Inside?
- 23 hours + Learning Videos for all Course Objectives (100% Course Covered)
- 13 Scenarios based Lab-Sessions
- Latest Updated content
- Unlimited Lifetime access
The AWS Certified Security Specialty Online Course covers the following topics –
Course Introduction (5)
- The Course Overview
- Certification Benefits Recap
- Also, Understanding the Shared Responsibility Model
- Birds-Eye View of AWS Security
- Finally, Setting up Your AWS Environment
Understanding Infrastructure Security – Part One (4)
- Firstly, Using Key Pairs with EC2 Instances
- Understanding Hypervisors and Isolation in EC2 Instances
- Get to Know AWS Secrets Manager
- Finally, Leveraging AWS Systems Manager, Parameter Store, and Run Command Features
Understanding Infrastructure Security – Part Two (3)
- Firstly, What Is a VPC?
- Enabling Safe Internet Connectivity in VPCs
- Finally, AWS Marketplace Security Products
Leverage AWS Services for Logging and Monitoring – Part One (3)
- Firstly, Enabling Centralized Logging with CloudWatch
- Leverage CloudTrail to Track User Activity and API Usage
- Finally, Using Athena to Query Your Logs
Leveraging AWS Services for Logging and Monitoring – Part Two (3)
- Firstly, Automated Security Assessments Using AWS Inspector
- Intelligent Threat Detection Using AWS GuardDuty
- Finally, Benefits of Using a Trusted Advisor
Deep Dive into AWS Identity and Access Management – Part One (3)
- Firstly, Overview of AWS IAM for User and Group Management
- Deep Dive Into AWS IAM Roles and Policies
- Finally, Using AWS Organizations and Service Control Policies
Deep Dive into AWS Identity and Access Management – Part Two (2)
- Firstly, Enabling Active Directory Federation Within AWS
- Then, Understanding Cognito and Web Identity Federation
Ensuring Data Protection – Part One (4)
- Firstly, Using AWS KMS to Easily Manage Data Encryption
- Hands-On KMS
- Restrict Access to S3 Buckets Using Policies and Pre-Signed URLs
- Finally, Enabling Vault Lock in AWS Glacier
Ensuring Data Protection – Part Two (3)
- Firstly, Force S3 to Use CloudFront
- Getting to Know AWS Certificate Manager
- Finally, Security Considerations and Features of AWS Load Balancers
Managing Incident Response (4)
- Firstly, Overview of a DDoS Attack
- Enabling AWS WAF and Shield to Protect Against DDoS Attacks
- Configuring Throttling and Caching in API Gateway
- Finally, Managing Compliance Requirements in AWS Using Artifact and Macie
Final Preparation (3)
- Firstly, Booking Your Exam Seat
- Exploring Relevant Whitepapers
- Finally, Uncovering Additional Tips
With this, you have now included every domain covered in the AWS Security Specialty online course. Now, it is time to brush up the skills you’ve acquired via this online course. Sharpening your skills will help you master them, and will therefore serve very beneficial in grabbing highly paid job profiles, and other financial benefits.
Benefits of AWS Security Specialty Online Courses
Since online Course or e-learning, in general, has opened avenues for a lot of opportunities to bolster professional skills. Professionals also prefer to manage their preparation at their own pace. Nowadays, online learning is an increasingly popular option for candidates who have chosen to return to full-time or part-time study. In the same vein, let’s view some of the benefits:
- One of the clear advantages of online courses is that you can easily control and plan your own study schedule.
- Similarly, since you’ll be studying from home, you don’t have to worry about traveling to attend classes. Plus, if you have a physical disability or can’t travel to a physical classroom for logistical reasons, online learning enables you to keep progressing in your education.
- Overall, the cost associated with Online learning is comparatively lesser than class-room training
How AWS Security Specialty Online Course will benefit you?
We at Testprep Training are proud to say that our free practice tests and Online Courses have always been in demand. With the aim of aiding candidates to qualify for the certification exam, we offer world-class training material. The following points mention how Testprep Training online course will help you in your exam preparation.
- The principal focus of the AWS Certified Security Specialty Online Course is to provide complete course coverage. Besides this, we keep on updating our material. Once you complete the training course, you will be well-versed with the required skills and knowledge.
- Subsequently, the online videos are detailed and comprehended in a professional manner. You can complete a topic whenever you have even little time in your busy schedule.
- The training course comes with lifelong validity and unlimited access. Also, if there is any change in the exam objectives, we keep on updating the course content. As a result, you get access to the newly added training videos.
Preparation Resources for the AWS Security Specialty Exam
Let’s start by exploring the resources that are available to help you pass the exam and achieve your certification on your first try in the AWS Certified Security Specialty Study Guide.
Official AWS Training
The Official AWS Certified Security Specialty training Training will guide you to pass your certification tests on your first try. There are a lot of choices with regards to preparing up your AWS CSS Exam voluntarily, at your own pace. AWS itself distributes piles of preparing and training materials on its site. The courses there will assist you in getting ready for the exam by investigating the domains and planning your study accordingly.
AWS Certified Security Specialty White Papers
When preparing for the AWS you can also take the help of amazon whitepapers for preparation. The whitepapers are the authentic study resources that we can surely vouch for. These are basically the pdf formats of the topics which you can find on the official page of amazon certifications. Whitepapers not only strengthen your preparation process but also helps you build a strong strategy to lay your focus on. AWS provides sample papers to help candidates gain extra knowledge and skills for their certification exam preparation.
Online Tutorial
Another important learning resource to qualify the exam and gain expertise is the AWS Certified Security Specialty online tutorials. These tutorials provide a well-elaborated study guide that’ll assist you in gaining hands-on proficiency in applying the concepts of the AWS Security platform in practical scenarios, as an AWS Certified Security Specialist.
Exam Books
AWS Certified Security Specialty Books are undeniably the most reliable source of information. Referring to the relevant books will not only help gain knowledge but will also clear all your queries. Here is a list of some highly recommended books –
- AWS Certified Security Specialty Workbook: Exam SCS-C01 by IP Specialist
- AWS Certified Advanced Networking Official Study Guide: Specialty Exam by Sidhartha Chauhan
- Mastering AWS Security: Create and maintain a secure cloud ecosystem by Albert Anthony
- AWS Certified Security – Specialty Exam Guide: All you need to know to clear the AWS Security specialty exam by Stuart Scott
Practice Exams
The AWS certified security specialty practice exam is your final step. Practicing will help you identify the level at which you are and how much preparation do you need. You can find many reliable sites that offer many free practice tests and paid test series. Take a free test now!
Although, there are many AWS Training courses and other resources to aid you with collecting added knowledge and skills to qualify this certification- hands-on experience will always top the list. Whether you are a fresh graduate, or a self-taught guy, or a settled expert, getting AWS certifications is the way to go. You’ll boost your chances of securing down that dream job, gain higher salaries, and also get that industry-recognized stamp of approval marking you out as an AWS Certified Security Specialist.




